I used to be trying to find a reliable Linux web hosting support and stumbled upon the Server Basket internet hosting site. I used to be amazed by their company. Been utilizing the Linux KVM web hosting for months and under no circumstances confronted any concerns with my Internet site.
If you discover committed internet hosting way too high-priced but shared internet hosting can not satisfy your requirements, cloud VPS strikes an ideal equilibrium. It provides dedicated means for best performance without the high fees associated with focused servers.
Our VPS servers are well guarded all the time. Your privacy can also be Protected as we also don’t use third-celebration cookies on our site and also have our individual BTC payment implementation!
In the event your solutions are remaining on the internet with out DDoS defense, They are really liable to sudden interruption at any time. DDoS assaults are an
These attacks operate mainly because for an unprotected system it may be complicated to distinguish involving genuine targeted traffic and DDoS site visitors.
Nevertheless, it may well acquire minimal additional if you'll find few a lot more orders in the queue or whether it is a weekend or in the event that your get is flagged as high possibility and involves guide critique.
I've uncertainties about this. I imply, i’ve hosted my own OpenVZ before on devoted to respond to some performances desires I'd. Regardless of whether it’s not that a lot, OpenVZ was more impressive than KVM on the same committed. It’s also a thing i’ve observed when i’ve labored for any huge hosting enterprise.
Thinking of you now realize that you might want to use the mangle desk and also the PREROUTING chain as well as optimized kernel options to mitigate the results of DDoS assaults, we’ll now move on to a handful of example guidelines to mitigate most TCP DDoS assaults.
If you choose a JavaPipe product, you don’t have to bother with these items anymore and it’s often a greater substitute to remote security and presents higher uptime than the rest.
As it is possible to see you can find four distinctive tables on a mean Linux process that doesn’t have non-typical kernel modules loaded. Just about every of those tables supports a different list of iptables chains.
For those who don’t need to duplicate & paste Each individual solitary rule we talked over on this page, you can use the beneath ruleset read more for simple DDoS security of your Linux server.
Certainly, we can assign an inside nearby IP tackle to your whole servers and use firewall regulations to the outside community.
LowEndBox has released an in-depth frequently requested concerns write-up on virtual non-public servers, why you would like a cheap VPS, and much more. Also check out our Group message board, LowEndTalk, where 1000s of consumers are joyful to reply questions.
KVM rocks, that's the only way to state it. Seriously there nothing much better for virtual servers. But I still want that it may individual CPU threads superior but probably that may be impossible with out dedicated CPU chip.
 Scott Baio Then & Now!
Scott Baio Then & Now! Richard "Little Hercules" Sandrak Then & Now!
Richard "Little Hercules" Sandrak Then & Now! Romeo Miller Then & Now!
Romeo Miller Then & Now!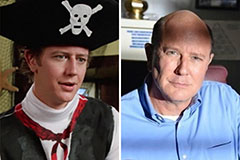 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Keshia Knight Pulliam Then & Now!
Keshia Knight Pulliam Then & Now!